Incident Summary
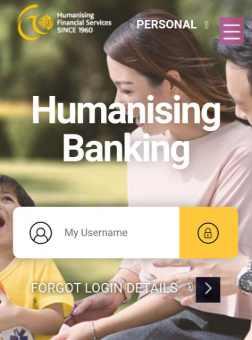
The XFarisX phishing case is a simulation based on real cybercrime tactics seen in Malaysia. This fictionalized scenario is designed to raise awareness by mimicking a large-scale credential theft attack. The group behind it impersonates legitimate bodies like LHDN and local banks, sending out fraudulent messages via SMS and email.
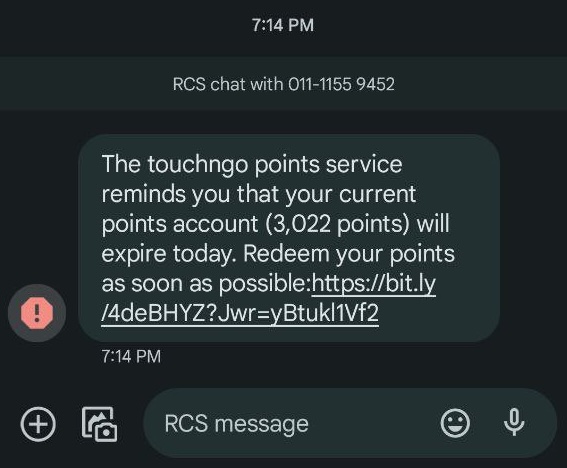
Through cloned websites and stolen branding, they trick victims into entering sensitive data such as banking details, IC numbers, and OTP codes. Our investigation reveals coordinated efforts involving spoofed SMS gateways, fake domains, and hidden Telegram marketplaces used to sell the stolen data.
Case Details
Key Suspects
 PRIMARY SUSPECT
PRIMARY SUSPECT
Wan Ahmad Faris
Skilled in web cloning, domain spoofing, and bulk SMS phishing. Believed to be the main perpetrator behind this campaign. Uses VPNs and foreign hosting to conceal identity. Also suspected of selling stolen data on Telegram.
- Connected to 8 cloned domains mimicking LHDN and local banks
- Phone number traced from phishing OTP scam matches VPS registration
- Operated multiple Telegram groups selling stolen bank logins
 PERSON OF INTEREST
PERSON OF INTEREST
Zhang Wei
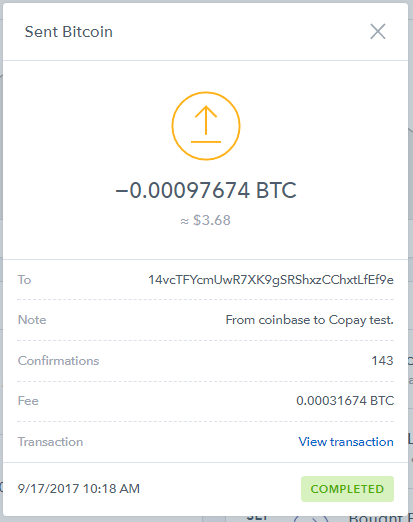
Launders stolen funds through crypto exchanges and mixing services. Acts as middleman for converting stolen credentials into crypto. Connected to multiple wallet addresses flagged in this investigation.
- Blockchain tracing shows stolen funds sent to wallet under alias
- Wallet used crypto mixers and foreign exchanges (non-KYC)
- Found in transaction chain related to OTP theft proceeds
 PERSON OF INTEREST
PERSON OF INTEREST
Aisha Binti Abdullah
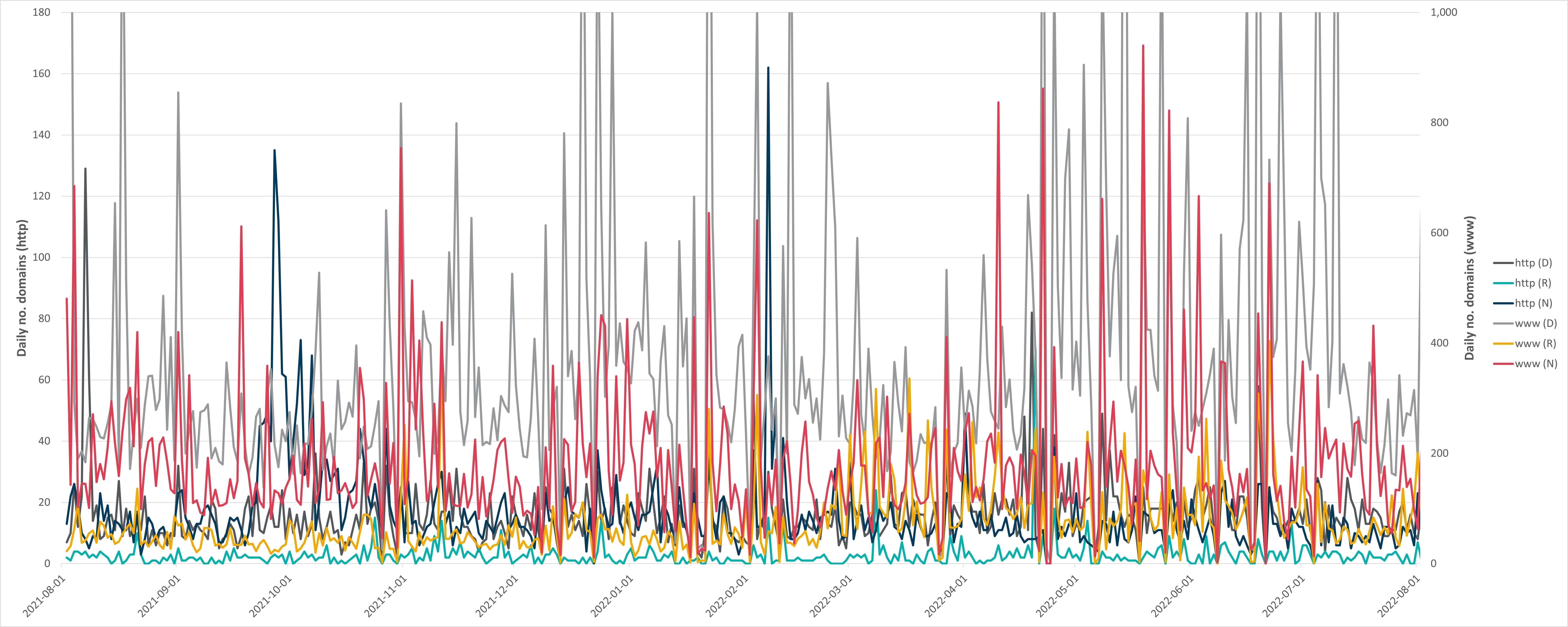
Technical specialist in bulletproof hosting services. Helped register phishing domains and maintain infrastructure, including fast-flux DNS to hide real locations.
- Registered phishing domains using bulletproof hosting services
- Hosted fast-flux DNS servers for scam website evasions
- Logs shared by hosting provider confirm activity under alias
 CLEARED
CLEARED
Nigel Kumar
Initially suspected but had verified alibis. His digital footprint and timeline didn’t match the phishing operation.
- Verified alibi during major SMS phishing periods
- No digital trail linking to XFarisX or domains
- Device forensics showed no malware or phishing kits
 CLEARED
CLEARED
John Pork
Although initially flagged due to similar attack traces, forensic analysis confirmed no connection to phishing domains or financial trails.
- Hosting overlap was coincidental; different customer account
- No transactions linked to any stolen funds or BTC trails
- Fingerprint analysis shows mismatched attack patterns
 CLEARED
CLEARED
Sum Ting Wong
No phishing software or traceable digital trails linked to her devices. All access logs showed mismatches with the timeline of the attacks.
- No phishing tools or links found on devices
- IPs didn’t match attack servers
- Alibis verified, no financial ties
Case Timeline
First Victim Report
First victim reports unauthorized deduction after SMS claiming tax refund.
Domain Cluster Identified
8 fake LHDN domains discovered, linked by WHOIS data to alias XFarisX.
Infrastructure Analysis
Hosting found using fast-flux DNS from Eastern Europe.
Money Trail Found
Blockchain trail identifies crypto laundering by alias "DarkWei".
Case Officially Opened
Spring Security officially launched to analyze phishing behavior.
Hosting Provider Cooperation
Hosting provider confirms alias "PhantomPhisher" managed phishing domains.
Current Status
Status: Still under active investigation in simulation environment.
Digital Evidence